Cyber Incursions: Erosions of Security and Social Trust?

Spring 2008 Conference Description
University of Virginia
Charlottesville, Virginia
March 30 to April 1, 2008
Conference Overview
Society continually finds itself more and more dependent on the internet for personal, corporate, and government use; with increased application in both the public and private sector comes increased activity and opportunity for criminal enterprises. Despite the enormous importance placed upon it, the internet lacks the proper defense mechanisms to effectively combat cyber incursions, or intentional compromises of web security. Humanity has accomplished feats of physical defense, yet it has overlooked the protection of the cyber field. As developing nations acquire and improve internet technologies, the potential for illicit and potentially martial activity grows exponentially causing the cyber field to emerge as a focal point of hostile activity. Therefore, the Critical Incident Analysis Group addressed internet security as the topic of their eleventh annual conference, “Cyber Incursions: Erosions of Security and Social Trust?”
Conference Highlights
Distingtuished Guests
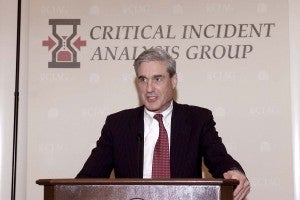
- Robert Mueller – Director Mueller was appointed the sixth Director of the Federal Bureau of Investigation by President George W. Bush in September 2001. He joined the Department of Justice initially in 1989 as an Assistant to Attorney General Richard L. Thornburgh. Named United States Attorney in San Francisco in 1998, Mr. Mueller held that position until 2001 when he served briefly as Acting Deputy Attorney General of the United States Department of Justice before becoming the current FBI Director.
- Charles S. Robb – Senator Robb served as Lt. Governor to the state of Virginia from 1978 to 1982 before being elected Governor in 1982. After his term ended in 1986, he chaired numerous committees, including the Southern Governors’ Association, the Democratic Governors’ Association, and the Education Commission of the States, among others. In 1989 he was elected to the United States Senate where he served Virginia until 2001. Since 2001, Senator Robb has taught at George Mason University as a Distinguished Professor of Law and Public Policy.
- Anita Jones – Currently the Lawrence R. Quarles Professor of Engineering & Applied Science and a Professor of Computer Science for the University of Virginia, Professor Jones functioned as the Director of Defense Research and Engineering at the Department of Justice from 1993 until 1997. In addition to teaching at UVA, Prof. Jones currently serves on the MIT Corporation Executive Committee as well as the Board of Directors of Science Applications International Corporation, BBN Technologies, and In-Q-Tel.
- Ambassador Nathaniel Howell – Ambassador Howell is currently the John Minor Maury, Jr. Professor of Public Affairs at the University of Virginia. He is also the Director of the Institute for Global Policy Research as well as the Arabian Peninsula and Gulf Studies Program. Amb. Howell served as Ambassador to Kuwait from 1987 through 1990 and has been presented with numerous awards, including the Presidential Meritorious Service Award for members of the Senior Foreign Service in 1991 and the Secretary of State Award for Valor in 1977 and again in 1991.
- William Wulf – Presently the AT&T Professor of Engineering in the Computer Science Department of the University of Virginia, Professor Wulf took a leave of absence from the University from 1996 until 2007 to serve as President of the National Academy of Engineering. He has authored or co-authored three books, holds two patents, and has written over 100 papers.
- John O. Marsh, Jr. – Former Congressman Marsh served Virginia’s Seventh Congressional District from 1961 until 1971. After serving as a Counselor to President Gerald Ford, he was appointed Secretary of the Army, holding the position from 1981 to 1989. He has taught cyber-law in multiple arenas, including George Mason University, the College of William and Mary, and the Virginia Military Institute, where he is currently a member of the Board of Visitors.
- Edwin Meese, III –Mr. Meese served as Counselor to President Ronald Reagan from 1981 until 1985, after which he was appointed Attorney General, a post he held until 1988. Currently, Mr. Meese holds the Ronald Reagan Chair in Public Policy at the Heritage Foundation where he is also the Chairman of the Center for Legal and Judicial Studies. He is also a Distinguished Visiting Fellow at the Hoover Institution at Stanford University.
- Shawn Henry – Mr. Henry began his career with the FBI in 1989 as a special agent investigating public corruption and as a member of the FBI SWAT tram. In 1999 he was chosen to be a representative of the United States’ delegation at the G8 conference in Cologne, Germany, in the High-Tech Crimes Subgroup. Mr. Henry was appointed the Assistant Director of the FBI’s Cyber Division and is currently serving as the Assistant Director in Charge of the FBI’s Washington Field Office.
Key Panels and Discussions
The discussions focused on the innate vulnerabilities of the internet itself, both technological and sociological in nature. While the necessary technological implements to safeguard the data trusted to the internet are lacking, security is also hindered by the human element that resides in front of the keyboard. The discussion identified four major points of vulnerability: ease of access to data, anonymity of users, decoupled locale, and the speed with which data is transacted. While these elements are potential vulnerabilities, they are not necessarily weaknesses. Those who take advantage of these facets for ill are subject to similar manipulations by law enforcement.
On a global front these vulnerabilities present unprecedented issues and scenarios. The anonymity of users combined with the obscurity of their locations hinders investigations and causes difficulty in distinguishing the character of a crime, crippling the designation of legal responsibility. Distinguishing between cyber-terrorism, cyber-warfare, and vandalism becomes difficult, if not impossible, and often prevents officials and governments from taking the necessary action to prescribe justice. In one incident described in the conference, an Eastern European country’s networks were gridlocked by virtual protestors, inciting a “cyber riot” and causing the country’s internet to be temporarily shut down. Although investigators later revealed some attacks were instigated by a neighboring country’s government, the extent to which these attacks were state-sanctioned is still unclear. Issues such as these are only reinforced by a lack of clear legal doctrine regarding cyber attacks and are further magnified by a general reluctance in the global community to collectively pursue a unified agreement in the matter.
With data security dependent upon millions of lines of software code, protection is still technologically inadequate. Hackers need only to find a single flaw within a code sequence to exploit it, using it to their advantage. Therefore, the mindset of those who engage in internet security must be radically changed from perimeter defense to more mobile, preventative means. At the same time, the human element must not be overlooked. In addition to proper technological protections, users must be diligent in their awareness of dangers presented to them. When technological and human errors work in tandem, the result can be disastrous. In the three case studies analyzed, including the affair involving the Eastern European country described above, errors from machine and man permitted the incursion of hostile agents who profited personally as well as ideologically. Overall, revision of internet protocol is currently needed in order to properly safeguard future internet users. Recommendations emphasizing the need for action by the public, private, and academic sectors in an effort to help bolster the security inadequacies currently in place were generated in response to the growing global threat. As FBI Director Robert Mueller remarked, “We do not protect cyber space as well as we protect our physical space. We have left doors open.”
Representative Insights
“It [is] as though we were [living] 60 or 70 years ago and really appreciating the value of nuclear power to produce energy, but being completely oblivious of the possibilities of nuclear warfare. And just now, we’re beginning to realize that there is a downside to all of this, that there are difficulties that we’ve got to be careful about.” – John, Lord Alderdice, MP
“We used to think of warfare in terms of nation-states taking action. But now, in fact, an individual can levy war against another, against a corporation.” – Anita Jones
“The core of the internet only promises best effort delivery.” – William Wulf
“The least understood dimension of the cyber problem, in my opinion, is the human dimension…The common element in all of the successful attacks was the human element. Somebody had made a mistake.” – Robert Dannenberg
“You just can’t protect everything…If we defined everything [that] needed to be protected, we’d be able to protect nothing.” – Rolf Mowatt-Larssen
“The Internet has opened up thousands of new roads for each of us – new ideas and information, new sights and sounds, new people and places. But the invaders – those whose intent is not enlightenment but exploitation and extremism – are marching right down those same roads to attack us in many ways.” – Robert Mueller
Conference Images
- Anita Jones raises a point of discussion during an afternoon break-out session.
- FBI Director Robert Mueller addresses the Conference Members.
- Leonard Sandridge, University of Virginia Chief Operating Officer addresses the group following dinner.
- Chuck Robb, Distinguished Professor of Law and Public Policy at George Mason University, speaks at a round table discussion.
- Shawn Henry speaks at a round table discussion.
- Susan Smith, Chief of the Risk Development for Department of Homeland Security, and Chris Holstege hold a sidebar conversation during a session break.
- Hon. Ed Meese addresses the group as John, Lord Alderdice listens on.
- Greg Saathoff, Ed Meese, David Kestenbaum, and John, Lord Alderdice hold a discussion during the evening reception.